Friday, June 1, 2012
Automated Warfare and the Offense vs. Defense Conundrum
On June 1, intelligence expert and ace reporter David Sanger offered up a front-page story in The New York Times revealing that the ultimate source of the Stuxnet (and presumably, Flame) worms and viruses was not Mossad Unit 8200 or the Likud Party, but President Obama, working through the National Security Agency and Cyber Command. It came two days after another NYT front-page story (this one not by Sanger) indicating that the president himself approved the targets for drone strikes in Pakistan.
Given the way the Justice Department has gone after journalists under Espionage Act prosecutions, one might think Sanger at least, and possibly Jo Becker and Scott Shane, have reason to be concerned. But wait - the White House deliberations described by Sanger sound very much like inside baseball. Could it be that Obama campaign managers leaked both stories in order to give the president an aura of military resolve? If so, it could end up being effective for his campaign. Cyber war is seen by many as victimless, and drone war is interpreted by many as a way to get the bad guys while hiding the blood. Obama not only can get troops out of Iraq and Afghanistan, he can tout himself as the master of the new automated robot wars. A lot of liberals and conservatives alike see that as an unabashed good thing.
You know I couldn't let that one go without comment, but the rant in this case is not merely a means of exercising sour grapes. In the case of cyber war, the methods of cyber defense practiced by NSA and Air Force Space Command/Cyber Command over several decades can have few critics. But the lesson with past computer war-games is that cyber-defense almost always is combined with cyber-assault. In this respect, it is much like the arcane arguments over missile defense and missile offense. Most U.S. citizens would say, "Let's use our advantages, and see cyber assault as preferable to real-world military assault." If that is the rationale, let us remember that no assault comes without expanding the footprint of results under the Law of Unintended Consequences. This happened with Stuxnet when the computer worm moved far outside the Siemens embedded controllers for which it was designed. Similar worms and viruses that impact critical safety systems and public utility systems are bound to have negative consequences as well. Protecting U.S. critical systems against hackers from China is a safe and prudent operation. Engaging in cyber assault has ethical implications that cannot be swept under the rug by saying that Stuxnet is better than bombs from Tel Aviv.
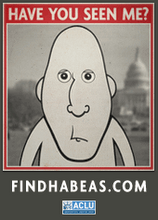
Such ethical consequences are even greater when one uses the precise targeting power of armed drones to craft the drone as a tool of targeted assassination. Sure, a drone is safer than a SEAL Team 6 that goes in-country to take down al-Qaeda operatives, and much safer than a large scale CIA or Special Ops assault. But the CIA and military intelligence agreed in 1976 not to engage in targeted assassination. This pledge was ripped apart by Dick Cheney when he hired Blackwater to create the kind of hit squads later used by Obama to get Bin Laden. The abrogation of the deal was regularized by President Obama in February 2009, when he developed regular lists of Pakistani and Afghan bad guys to take out of commission. Maybe this is a good thing, a cheap, sanitized, and relatively secret way to take down al-Qaeda one terrorist at a time. But you and I never voted on removing the assassination ban. This was simply considered fair game in the highly-touted War on Terror.
What President Obama has become expert in, might be called the new face of war. It is highly automated, quite secret, and very asymmetric. Who knows, maybe an attack by a flock of drones might be used against Baath officials in Syria, as might a computer assault on public utility systems. But asymmetric advantages are unstable by nature. Cyber war and drone war virtually guarantees blowback, which might include direct robotic assault on the U.S. homeland. Before blowback happens, it is useful to remind U.S. citizens that assault remains assault, whether it is conducted by bomber, JSOC squads, drones, or a computer virus.
Subscribe to:
Post Comments (Atom)








No comments:
Post a Comment